 Keychain is a password management system for macOS and iOS that was originally released with Mac OS 8.6 back in 1999 as a way of holding passwords, private keys, certificates and secure notes in encrypted files on the machine. Since then, Keychain has expanded to Apple’s mobile devices and synchronizes keychain files between devices through iCloud. This Tech 101 article explains the functions of Keychain in macOS Sierra as well as how to access and edit Keychain files.
Keychain is a password management system for macOS and iOS that was originally released with Mac OS 8.6 back in 1999 as a way of holding passwords, private keys, certificates and secure notes in encrypted files on the machine. Since then, Keychain has expanded to Apple’s mobile devices and synchronizes keychain files between devices through iCloud. This Tech 101 article explains the functions of Keychain in macOS Sierra as well as how to access and edit Keychain files.
What Does Keychain Store?
Keychains were originally developed in the early 1990s for use with an Apple email system called PowerTalk. The idea was that PowerTalk could communicate with many mail servers and online services, so it would use a keychain file to hold user authentication information within the application to automatically and securely log the user into the variety of services. With the creation and release of Mac OS X in the early 2000s, Keychain became part of the operating system and was used to hold much more information.
Keychain can hold passwords for websites, web forms, FTP servers, SSH accounts, network shares, Wi-Fi networks, groupware apps, encrypted disk images and more. The passwords are dynamically linked to a particular user’s login password, so that when the user logs into a Mac, all of the various accounts and passwords are made available to the operating system and select applications. Keychain also manages root certificates, keys, and secure notes.
Where Can The Keychain Files Be Found On My Mac?
Under macOS Sierra, the keychain files are stored in ~/Library/Keychains, /Library/Keychains/ and /Network/Library/Keychains/. These files are viewed and edited through an application called Keychain Access, found in the Utilities folder in the Applications folder. There’s also a command line equivalent to Keychain Access: /usr/bin/security .
These keychain files store several data fields including a title, URL, notes and password. While the title, URL and some other fields are plaintext, the passwords and Secure Notes are encrypted with Triple DES.
Common keychains include login, iCloud, System and System Roots. The login keychain is unlocked upon login, while the other keychains can be unlocked by clicking on their icons in Keychain Access, clicking on the “lock” icon, and then entering the administrative password for the Mac.
What Can I Use Keychain Access For?
Since it holds a lot of important information, the Keychain Access app should be used sparingly. However, it’s a useful place to recover passwords that you may have forgotten, get details on secure certificates, and to keep secure notes that you don’t want anyone to see.
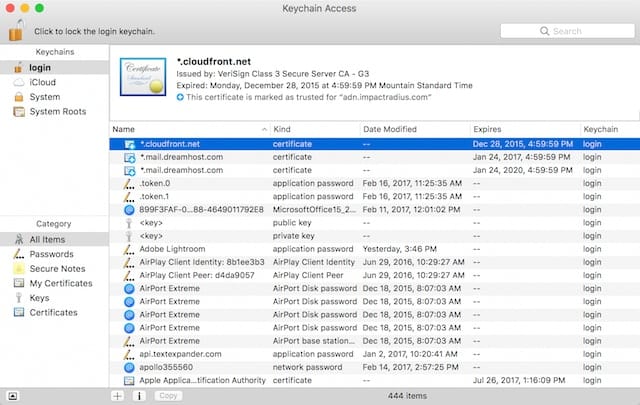
In the screenshot seen above, I’ve launched Keychain Access and I’m currently looking at the unlocked login keychain. It shows a number of application, network, internet and web form passwords; public and private keys used to encrypt/decrypt messages, and certificates.
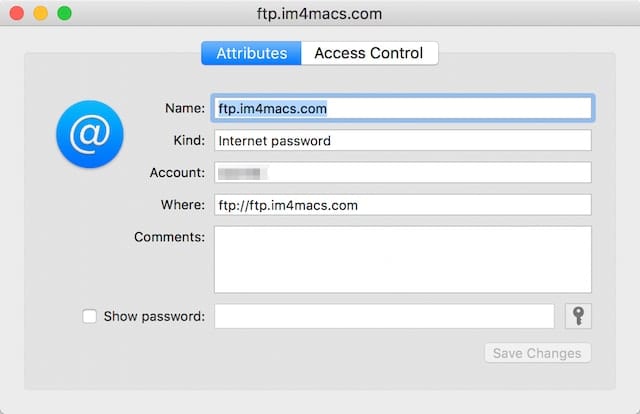
Let’s say that there’s a password that I’ve totally forgotten and haven’t stored somewhere else, like in a third-party password management application. For this example, I’ve misplaced my password for an old ftp server, so I scroll through the list until I find an entry for ftp.im4macs.com that is tagged as “Internet password”. Double-clicking the entry, the following window appears:
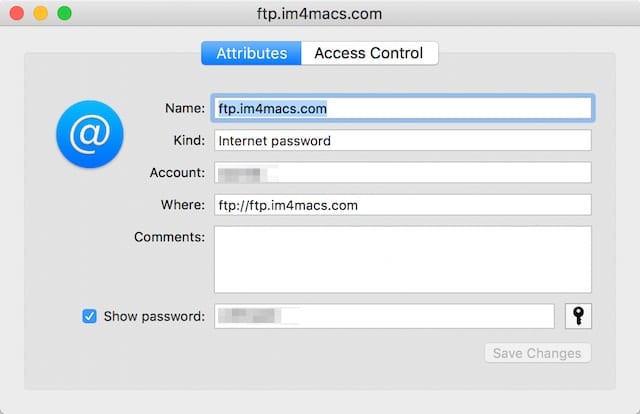
See the field at the bottom that says “Show password”? Check the box next to it, and a dialog appears asking for the login keychain password — that’s going to be the password you use to log into your Mac. Type it in, then click “Allow”, and the password becomes visible in the field next to the checkbox:
If I’d like to create a new password for that FTP site (of course, I’d have to change it on the FTP server as well), clicking the key icon at the far right of the password field displays the Password Assistant, which can be used to create new and very difficult to break passwords. Here, I’ve told it to create a “memorable” password of 20 characters length:
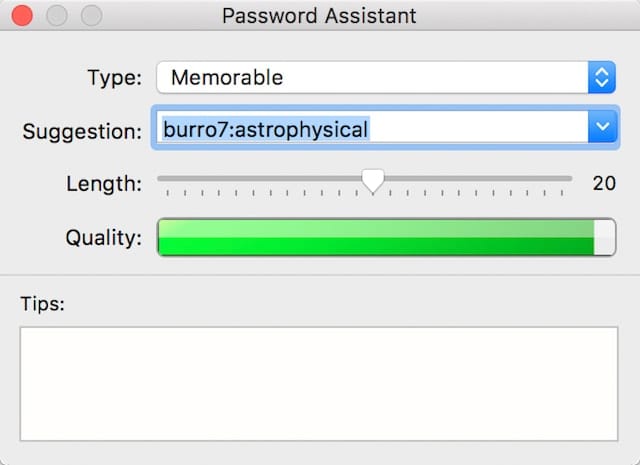
Twenty characters is pretty long, and it has suggested “burro7:astrophysical” as a password. Clicking the Save Changes button in the Attributes window saves the newly-generated password.
One other common use of Keychain Access is to create secure notes. Of course, you can also create password-protected notes in the Notes application on Mac and iOS, but people know to look in Notes for “notes”. Not many people would think of looking in the Keychain Access utility for secure notes.
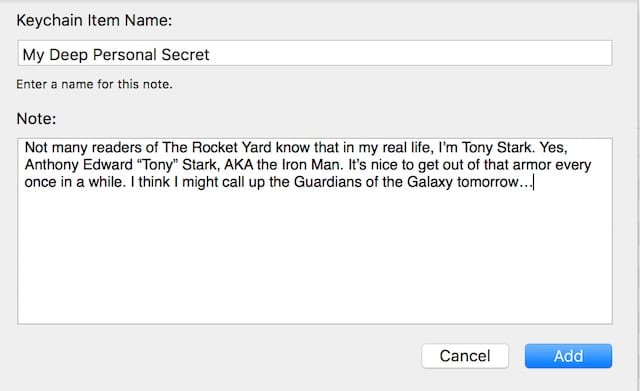
To create a secure note, click the item marked “Secure notes” under Category in the left sidebar of the Keychain Access window, then click the + sign at the bottom of the window. Type in a name for the Keychain Item, type in your note (see image below), and then click Add to store it as an encrypted secure note in your login keychain.
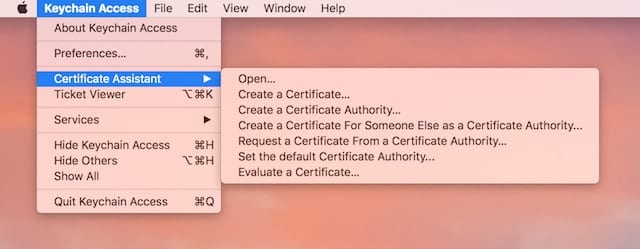
As part of our ongoing series on macOS Server, I’ve discussed the need to have certificates issued in order to secure your server. That can be done with Keychain Access. Although the process involved is rather detailed and beyond the scope of this post, note that by going to the Keychain Access menu and selecting Certificate Assistant, it’s possible to create certificates for yourself and for others (see image below):
What About That iCloud Keychain?
If you use use iCloud Keychain to synchronize passwords between all of the Apple devices you have tied to one iCloud account, then you can use Keychain Access to see what those passwords are by clicking on the iCloud item under “Keychains” in the left sidebar, then going through the process described earlier in this post to reveal a forgotten password.
Want to see the same information on an iOS device? There’s no Keychain Access utility for iOS, but just launch Settings, scroll down to Safari, then tap on Passwords. You’ll need to use Touch ID or your passcode to obtain access, but the next thing you’ll see is a list of websites for which you have stored passwords (see image below):
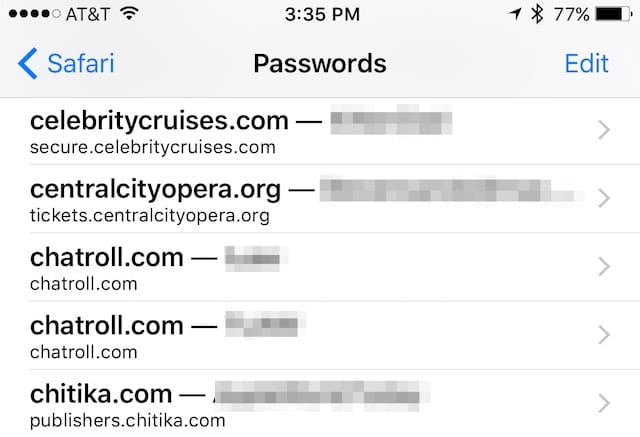
Tapping any one of those entries reveals a page showing the user name used on the website, the password, and the original website URL.
A Word Of Warning
Since Keychain contains so many passwords, encryption keys, certificates, and more, it’s not something that should be played with without a lot of respect. Don’t delete any entries unless you really know what they’re used for, don’t delete full keychains, and if you’re asked to verify any changes, think twice before committing to them.





Where do I read more about certificates? google added one on my computer last year when I took a G suite business email. It’s coming up for renewal I just notice…but I have no idea what to do. It was the person on the phone that did it. Do I have to renew, if so how? Help!!! :) Thx
I added a hard drive to my iMac and installed MacOS Sierra on the new hard drive about a year ago. I hesitated and delayed initiating Keychain (I thought) but now I cannot effectively use that operating system because Keychain keeps asking for a password to allow it to function but nothing works and I have no idea of whether I had already used one.
I hate keychains – they pop up every few seconds wanting my password! I don’t store any passwords on it! It locks all the time. Can I delete all?
HELP!!!!!
>While the title, URL and some other fields are plaintext, the passwords and Secure Notes are encrypted with Triple DES.
What makes you think apple is using triple DES?
Do you have a source for this information? It would seem exceedingly stupid for apple to use such a bad, out of date technology, but they’ve done so in the past IIRC (in filevault).
Quite right, Triple DES is dated and would not have been a good choice. Apple uses AES (see https://support.apple.com/en-gb/HT202303).
AES is fine. Apple also makes/uses processors with AES acceleration in hardware to reduce the encryption overhead.
I don’t feel my passwords are secure when they open with my computer by using the same password. Any technician working on my computer has access to all my accounts. I want to set up a different password for keychain. How can I do this?
Don’t give your password to technicians working on your Mac even if your employer owns the Mac. I am a Mac Sysadmin and technicians cannot access your keychain without your password. They can copy the keychain and back it up but if your Mac login password is a good strong one then not even a technician with the highest of privileges can access your keychain. Your personal keychain is stored in ~/Library/Keychains and it is heavily encrypted and locked with your Mac user account password. All your data inside that file is safe if your password is not compromised. A corporate technician can use their own account to login to your work issued Mac. If they need to help you with something inside your account then only you should unlock the Mac with your own password and stick around while the tech works on your Mac. If you are not present logout or lock the screen. You are responsible for backing your data if you take it to Apple for repair as well.
You can create a different keychain with a different password but it won’t be your login keychain. However you have to unlock it and lock it manually. You can add the keychain to the menu item bar to have easier access to it.
I’ve got an odd one, which hoepuflly will be fixed with High Sierra. I’ve got a handful of mac users that, intermittently, when they’re connected to a Windows share (smb) they lose their rights (get the red “no” circle on all folders). The quickest way to fix it is to delete their domain keychain, but it’s just a workaround. And it’s only with one particular share, all the others are fine. Can happen on wired, or wifi, if you disconnect and reconnect a bunch of times it ‘might’ fix itself, or it will just work out of the blue. odd…
Did you ever find a fix for this?
Thanks in advance.
my mac requires additional logins after I get to desktop. They require my old pwd. It asks for pwd for local.* … These are in effect items Apple no longer uses ..This was fixed at one point but updates brought it back ..
I’ve been a Mac user for many years and the Keychain utility has been a regular problem, often randomly but frequently during system updates. Once or twice a year some of the keychain icons would be greyed out or have a blank icon and were not accessible. Sometimes a restore would solve the issue but often not. Sometimes a time consuming manual rebuild was needed.
Some years ago due to the number of entries I began creating separate keychains to keep software activation keys and website credentials. The intention was to not mess with the default keychain. The problem persisted.
Recently I moved all my personal keychain items (software activation keys, website credentials, etc) to a non Apple solution. Things are much better now.
My keychain automatically creates numerous items.
Is this behavior due to my use with FireFox as a browser?
My knowledge isn’t very deep, yet, but if Keychain creates entries, I am not able to identify them. The section on certificates is a big unknown to me – maybe birth takes place there… In any case, they don’t seem to bother me so I leave them alone.
I am using Firefox, going on about 4 years.
Firefox does not interact/integrate with the keychain.
(BTW Chrome also dropped support for the keychain too).
I purchased a used Mac from OWC, made no changes to Keychain, always declining to add info to Keychain, I’m trying to understand it first. When I inspect my Keychain there are many entries. Those from Apple I’ll keep, others I don’t understand and I’m not sure if I should delete them. I’ve searched and can’t find a website that explains the purpose of non Apple Keychain entries. I need to either find out what the non Apple entries are, or what could happen if I delete all the non Apple entries. Websites state to inspect the entry, but the information is so general I still do not understand where it came from or its purpose.
On an earlier MAC I had Microsoft Office 2004. Using Entourage I frequently got a message “Entourage wants to use your Keychain”. I did not know what that meant, but always checked No. Why would Entourage want access to my Keychain?
Hi, Harold –
Microsoft usually gets a bad rap from Mac owners, although they have pretty much always followed Apple’s guidelines to the letter — even sometimes more than Apple. I may be wrong, but I think that Entourage was probably asking for Keychain permission in order to save email server passwords in the Keychain. Had you answered “yes” once, you might not have seen that message again. Now apps are usually better written and ask for that permission up front when the software is initially installed.
THanks for reading (and for commenting!),
Steve
That makes sense, thank you very much! I have always been somewhat bothered by that thought that I might have left an opening for hackers. Keep up the good work in Rocket Yard.
Thanks for the info.
… and can you comment on which approaches are likely to be usable across all of Mac/iphone/ipad?
Interesting tutorial! However there are a number of choices for storing data in encrypted format, such as 1Password or Paranoia Text Encryption. Can you comment on the relative merits of different approaches?
Hi, Ed. We will have an article covering third party choices next week, so stay tuned to the Rocket Yard :)
Why would one want to use Apple Keychain if they use a 3rd Party Password system like “1Password”.
A couple of reasons, Don. Some people don’t want to pay the subscription fee for 1Password, so the built-in Apple Keychain that’s usable in many situations across devices is a perfect — and free — example. In addition, many newbies don’t know about 1Password and similar apps/services, so Keychain is about the only service they might use. For those who DO use 1Password, Keychain is a good backup for those passwords and often auto-fills info much faster than 1Password will…
Thanks for the reply Steve.