 Earlier this week, we began a month-long series designed to bring Rocket Yard readers up to speed on networking and security. The series began with an article detailing DNS (Domain Name System), a critical component of the Internet. Today we continue with the series, unraveling the acronyms that describe Wi-Fi security methods, describing some ways that hackers can attack wireless networks, and defining other security measures that can help keep your data safe while using Wi-Fi at home or on the road.
Earlier this week, we began a month-long series designed to bring Rocket Yard readers up to speed on networking and security. The series began with an article detailing DNS (Domain Name System), a critical component of the Internet. Today we continue with the series, unraveling the acronyms that describe Wi-Fi security methods, describing some ways that hackers can attack wireless networks, and defining other security measures that can help keep your data safe while using Wi-Fi at home or on the road.
Why Do I Need To Secure My Mac, iPhone or iPad on a Wireless Network?
Just about every computer, smartphone, or tablet sold these days has Wi-Fi built in. It’s convenient, usually fast, and lets users enjoy the Internet without the need to be tethered to a wired network with an Ethernet cable. With that convenience comes a necessity to make sure you take the proper steps to ensure that your device and network are set up to keep your personal information from being “sniffed” by a relatively unskilled hacker.
The simplest way to secure your Wi-Fi network or device is to start by making sure that your wireless router (the device that connects to the Internet and allows your Wi-Fi enabled devices to connect) has some sort of Wi-Fi security turned on.
What Wi-Fi Security Standards Are Available?
Here’s where we start throwing out a few acronyms! Older Wi-Fi networks that require a password to get access to the Internet may use an out-of-date standard from 1997 known as WEP (Wired Equivalent Privacy). WEP is quite insecure, and passwords can be cracked in a few minutes with software widely available on a number of hacking websites with even the most basic of laptops. If your Wi-Fi router only supports WEP, it’s highly recommended that you install and use a more modern router than supports the newer security standards.
WEP was replaced in 2003 by WPA (Wi-Fi Protected Access) and in 2006 by WPA2, the second-generation of WPA. Most new routers no longer support WEP or WPA, using WPA2 instead as a protocol to encrypt data “in the air” between a Wi-Fi device and the router. Devices certified by the Wi-Fi alliance to carry the Wi-Fi trademark require support for advanced encryption methods that are part of the AES (Advanced Encryption Standard) standard. Those methods use 128-bit key encryption, meaning that it takes a long time for a brute force attack attempting to find the key (by guessing the key) to be completed.

WPA3 began rolling out in 2018 and not all routers or devices support the new, more secure standard yet. What are the features of WPA3? First, it uses what is called “individualized data encryption” on open Wi-Fi networks. This means that the traffic between your device and the Wi-Fi access point is encrypted, even if you never entered a passphrase when you connected to the network. This means that public, open Wi-Fi networks will be much more secure.
Next, WPA3 provides “robust protections even when users choose passwords that fall short of typical complexity recommendations.” This is important for one very big reason — it protects networks against brute-force attacks, where a malicious party attempts to guess at passwords over and over until the correct one is chosen and the encryption is cracked.
WPA3 should also make it much easier for devices without displays to connect to Wi-Fi networks. What we’re talking about here are home-automation devices and smart appliances, which currently require a smartphone app to connect to the network. As of yet, there are no details on how this is supposed to work.
Finally, the Wi-Fi Alliance has stated that WPA3 will have a “192-bit security suite, aligned with the Commercial National Security Algorithm (CNSA) Suite”. This won’t help out home users, as it is meant for government, defense, and industrial applications.
How Can Wi-Fi Security Be Compromised?
There are a lot of ways that a dedicated hacker can compromise Wi-Fi security and have access to your data. Here are just a few examples:
Accidental Association: This occurs when your computer attaches to a wireless access point that is not secured (doesn’t require a password to join) by accident. You may not know that this has even happened unless you occasionally happen to check the name of the network being used for connectivity. On a Mac, this can be done by clicking the Wi-Fi icon in the menu bar and looking for the active network, which will have a checkmark next to it. On iOS devices, check the active network by tapping on Settings and looking at the network name next to the Wi-Fi icon.
Malicious Association: You know how your Mac and iOS devices can be set up to share a network connection? On iOS devices, it’s called Personal Hotspot, while on the Mac it’s called Internet Sharing. A malicious hacker can easily set up a Wi-Fi network that looks like a legitimate network access point, giving it a name like “Free Airport Wi-Fi” or “Guest Wi-Fi”. Once the hacker has set up the fake network (called a Soft Access Point), he or she can even set up a fake password request page that’s similar to a known (Starbucks, AT&T, etc…) Wi-Fi access point, then grab user names and passwords.
Much more likely is that the hacker will allow access to the network without a password, then use a packet sniffer to copy and analyze whatever is being sent over the network — your user names and passwords, credit card numbers, and so on. In what is called a man-in-the-middle attack, the hacker forces your device to drop its connection to a real network and connect to the soft access point, at which point. you need to reenter your password again. There are widely available applications available that make these attacks easy for even beginning hackers.
MAC spoofing: Every device connected to the Internet has a unique MAC (media access control) address. Many companies — and even some home users — set up their wireless networks so that only specific devices with known MAC addresses can access the network. Unfortunately, in order to make itself known to the router or wireless access point, each device also broadcasts its unencrypted MAC address on a regular basis. A hacker can use a freeware packet analyzer application to obtain the MAC address of any device within range, then use that MAC address to appear to be a valid network user.
What Are Some Suggestions for Maintaining a Secure Wi-Fi Connection?
Despite the fact that it’s quite simple for a hacker to break into a Wi-Fi network and sniff packets to gather information, you can make your use of wireless networks much safer by implementing these easy security tips. Just think of it this way — if you make it more difficult to a hacker to break into your network, they may just try to find an easier target.
1 – Hide Your SSID
If you set up a Wi-Fi network in your home or office, you usually set up a unique SSID (Service Set Identifier). That’s the “name” of the network that you see when making a connection. While many people just leave the default name that comes from the factory (Belkin, D-Link, Linksys) or Internet Service Provider (Comcast, Xfinity, Century Link…), it’s much more common to give it a name you’re familiar with. One good way to prevent others from attempting to break into your Wi-Fi network is to just hide the SSID altogether.
Of course, if you are looking for your network and can’t see that SSID, how do you connect to it? Using MAC ID filtering or another similar method of only allowing access to specific client devices.
2 – Use MAC ID Filtering
Many routers and Wi-Fi access points let the owners set up a list of known, pre-approved MAC addresses. Using MAC ID Filtering, only those devices with MAC addresses that have been added to the list can connect to the Wi-Fi network. MAC ID filtering can be hard to maintain if you have a lot of Wi-Fi devices, as you’ll need to add them to the list (and remove old MAC addresses) frequently. In addition, MAC spoofing gives hackers a way to bypass this method altogether.
3 – Use Static IP Addressing
Most Wi-Fi routers and access points simply hand out IP addresses unique to that network using what’s called DHCP (Dynamic Host Configuration Protocol). You connect to a network, and you’re assigned an IP address from a range of valid addresses. By assigning each device a specific IP address in a limited range of addresses, an attacker can’t simply grab an IP address to join the network. Once again, this adds complexity to Wi-Fi network setup.
4 – Enable Encryption on the Router/Access Point and All Devices on the Network
The best — and the easiest — tool for keeping a Wi-Fi network secure is to enable encryption on your router or access point. Every Wi-Fi labeled router and access point made since 2006 supports WPA2 encryption, and it’s quite simple to turn on the feature and add a password to your network. To make it more difficult for hackers to guess your password, we recommend using a strong password generator like that available in 1Password or the macOS Keychain Access app.
Keychain Access is found in Applications > Utilities. Once it has been launched, click the iCloud Keychain in the left sidebar, then select File > New Password Item. A screen similar to the one seen below appears:
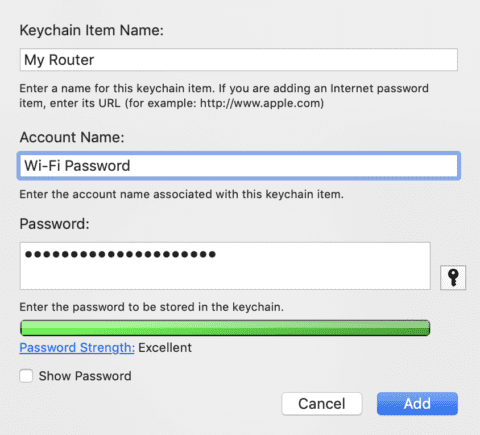
Type in a simple name for the Keychain item like “My Router” and type in an Account Name. Since routers do not require an account name, just type in something like “Wi-Fi Password”.
Click the key button, and the Password Assistant appears. To make it easier for you to enter a generated password into your router and type it in from your devices, choose Memorable as the type, then drag the length slider to the right until the password quality bar is completely green (see image below):

Close the Password Assistant, then click the Add button to add the password to your iCloud keychain for safekeeping.
WPA2 is “good enough”, but you might want to consider one of the other types of WPA2 algorithms. When setting up many routers, you’ll have a choice of “Security Mode”. Ignore the “open”, WEP 64, WEP 128, WPA-PSK (TKIP), WPA-PSK (AES) and even the WPA2-PSK (TKIP) options, as they are not as secure as WPA2-PSK (AES).
This latter algorithm is currently one of the most secure forms of WPA2. It makes use of the AES encryption protocol, and keeps all data between your devices and the router/access point fully encrypted at all times. If you have options for WPA2-PSK (TKIP) or WPAWPA2-PSK (TKIP/AES), you might want to pass on these as well as the TKIP protocol has known vulnerabilities.
5 – Use a Virtual Private Network (VPN) When Connecting to Public Wi-Fi
A Virtual Private Network or VPN provides a way to encrypt all traffic from your device to its destination on the Internet. We’ll cover VPNs in more detail in the third week of this series, but at this time it’s best to just say that VPNs are a must-have when you’re using public Wi-Fi.
Next week, we’ll cover the upcoming Wi-Fi 6 standard and how it will improve both speed and security for wireless networks. We’ll also describe a new model for network security that is called Zero Trust Networking — it’s beginning to catch on in enterprise.








Or just connect directly though ethernet……
One of the key improvements in WPA3 will aim to solve a common security problem.your website information is very helpful for everyone.
thank you
Thank you for this article as well as the one about DNS. It is a wonder that all these pieces actually allow such international communication/interaction.
I’m afraid your first 3 suggestions for making it “more difficult for a hacker to break into your network” are placebo (at best) or counterproductive, at worst:
1. Hiding your SSID just means that each associating client (i.e. each WiFi device) needs to broadcast it for the Access Point to respond, rather than the Access Point broadcast it. In the very rare case of a wireless network where devices rarely need to (re)associate this could be more secure. In the vast majority of cases there will be mobile devices (iOS, Android, laptops, etc) disassociating and reassociating all the time. Each time they do, they broadcast the SSID so that the Access Point can identify them and respond.
2. You identify in the article why MAC ID filtering is entirely ineffective for any hacker. The MAC is broadcast in plain text.
3. You mischaracterise what DHCP does. It only suggests IP addresses to clients. It can’t stop them from using another, and does not prevent a client from using an IP address of its choice. Indeed, many network admins will use this characteristic of DHCP to troubleshoot DHCP issues.
On the other hand, suggestions 4 & 5 are worthwhile.
Unfortunately, as with every other WiFi Alliance security protocol, this one was developed without open review.WPA3, like all of the others will have to undergo successive refinement until the bugs are fixed. Early shipping devices will absolutely require firmware upgrades to fix the currently known problems. I assume that by WPAX the WiFi alliance will wise up!